Automatic Application Identification
Applications
While it is pretty clear where machine and process data come from, this is not so obvious with applications. In fact, there is a tiny little bit of magic involved here – the operating system does not have a concept of applications, it only knows about processes. The fact that receiver.exe, concentr.exe and wfcrun32.exe form a logical application entity called Citrix Receiver is totally irrelevant to the OS. For that reason, other monitoring products do not bother with applications.
uberAgent is different. It automatically groups related processes to applications, because humans think in applications, not in processes – and uberAgent is designed for humans. When troubleshooting performance problems it is not enough to know that, say, SelfService.exe has a problem. You need to know that Citrix Receiver generates all those IOs. uberAgent shows you exactly that and makes it easy to analyze the impact your applications have on overall system performance.
How It Works (Windows)
Automatic application identification works for classic Win32 apps just as well as it does for Java applications, Universal Windows Platform (UWP) apps, and Windows services.
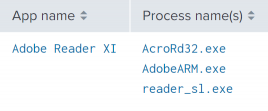
Win32
uberAgent determines the application names for all executables from properties of the MSI package the executable was installed from. Where that is not possible, uberAgent uses the information embedded in the executable.
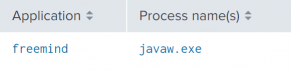
Java
uberAgent extracts the class name or filename of a Java command line. This works for Java Web Start processes, too.
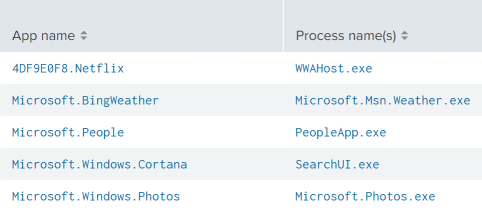
UWP
uberAgent retrieves the information from the UWP package.
Windows services
Starting with Windows 10 1703 each service gets a dedicated svchost.exe instance if certain minimum RAM conditions are met. uberAgent extracts the (localized) display name for services that run in a dedicated svchost.exe instance.
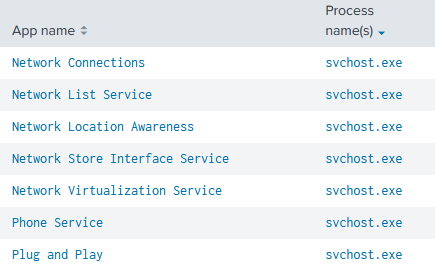
Requirements:
- Windows 10 1703 or higher
- uberAgent 5.2 or higher
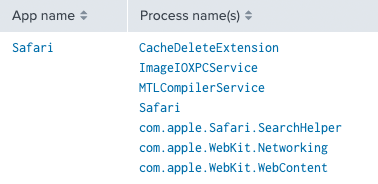
How It Works (macOS)
Bundles
uberAgent determines application names for executables that are part of a bundle folder structure by retrieving either bundle name, bundle identifier, or bundle executable name from the bundle’s Info.plist file. Executables located in nested app bundles are identified as their top-level host app bundle. Executables located in nested framework bundles are identified as their nested framework bundle, except for XPC Services which are always identified as the application that initiated their launch.
Executables
uberAgent extracts application names from executables that are not part of a bundle folder structure by retrieving either bundle name, bundle identifier, or bundle executable name from the embedded binary info plist. If an executable can not be identified this way but is located in a system directory it is mapped to app name macOS.
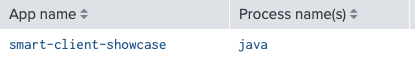
Java
In case a Java based application is not bundled, uberAgent extracts the class name or filename of a Java command line. This works for Java Web Start processes, too.
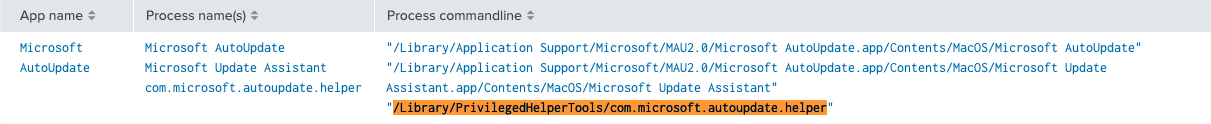
Privileged Helper Tools
uberAgent determines application names for executables located in /Library/PrivilegedHelperTools by inspecting their respective host app bundles as described above.
Configuration
Adding Your Own Mappings
uberAgent’s sophisticated method to map processes to applications works nearly every time for every application. When it does not, you can adjust it in the configuration section [ProcessToApplicationMapping]. Enter the full path to the process as a regular expression. Environment variables can also be used (enclosed in percent signs: %ProgramFiles%). Then specify the application name. Specifying only the file name without the full path works but is not recommended.
[ProcessToApplicationMapping] # App name for C:\Dir\my.exe is "MyApp" ^C:\\DIR\\my\.exe$ = MyApp # App name for all executables in "C:\Program Files\Windows Defender" is "Windows Defender" ^%ProgramFiles%\\Windows Defender\\.+\.exe$ = Windows Defender
Overriding Default Mappings
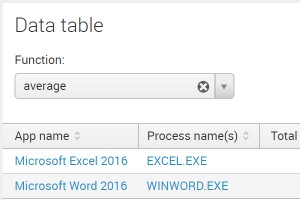
This configuration option also allows you to override uberAgent’s default mapping. Let us take Microsoft Office as an example. uberAgent, by default, groups all Office processes like WINWORD.EXE and EXCEL.EXE into the application Microsoft Office.
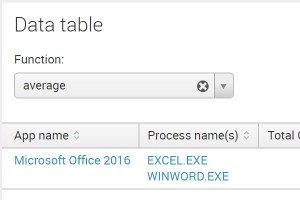
By changing uberAgent’s [ProcessToApplicationMapping] configuration settings as follows, you get individual applications per process.
[ProcessToApplicationMapping] ^%ProgramFiles(x86)%\\Microsoft Office\\root\\Office16\\EXCEL\.EXE$ = Microsoft Excel 2016 ^%ProgramFiles(x86)%\\Microsoft Office\\root\\Office16\\WINWORD\.EXE$ = Microsoft Word 2016
Ignoring Certain Processes
If you want uberAgent to ignore certain processes during application lookup, you can configure this with the option [ApplicationMappingIgnoredProcesses].
[/table-of-content]