Splunk Enterprise Security Integration
Splunk Enterprise Security
Splunk Enterprise Security (ES) solves a wide range of security analytics and operations use cases including continuous security monitoring, advanced threat detection, compliance, incident investigation, forensics, and incident response. Splunk ES delivers an end-to-end view of organizations’ security postures with flexible investigations, unmatched performance, and the most flexible deployment options offered in the cloud, on-premises, or hybrid deployment models.
Source: Splunk
Integrating uberAgent ESA
uberAgent ESA comes with native support for Splunk Enterprise Security. This article summarizes all related information in one place.
Installation
Detailed installation instructions can be found here. In short, you need to install the following uberAgent apps on your ES server:
- uberAgent_searchhead.tgz: contains uberAgent UXM CIM information
- uberAgent_ESA_searchhead.tgz: contains uberAgent ESA CIM information
- uberAgent_ESA_ES_companion.tgz: required for Splunk’s risk-based alerting. Available on Splunkbase.
CIM Support
Splunk Enterprise Security works with data sources from many different vendors. This diverse data set needs to be normalized to allow users to search and interact with it in a standardized way. Splunk uses the CIM data model to achieve that.
While uberAgent had CIM support for a long time, we have extended the integration greatly with uberAgent ESA. If you are used to working with Sysmon data in ES, you will notice no difference when switching to uberAgent. uberAgent supports all CIM fields populated by popular Sysmon add-ons found in Splunkbase, and more!

Visit our blog post about the CIM integration for details.
Risk-Based Alerting
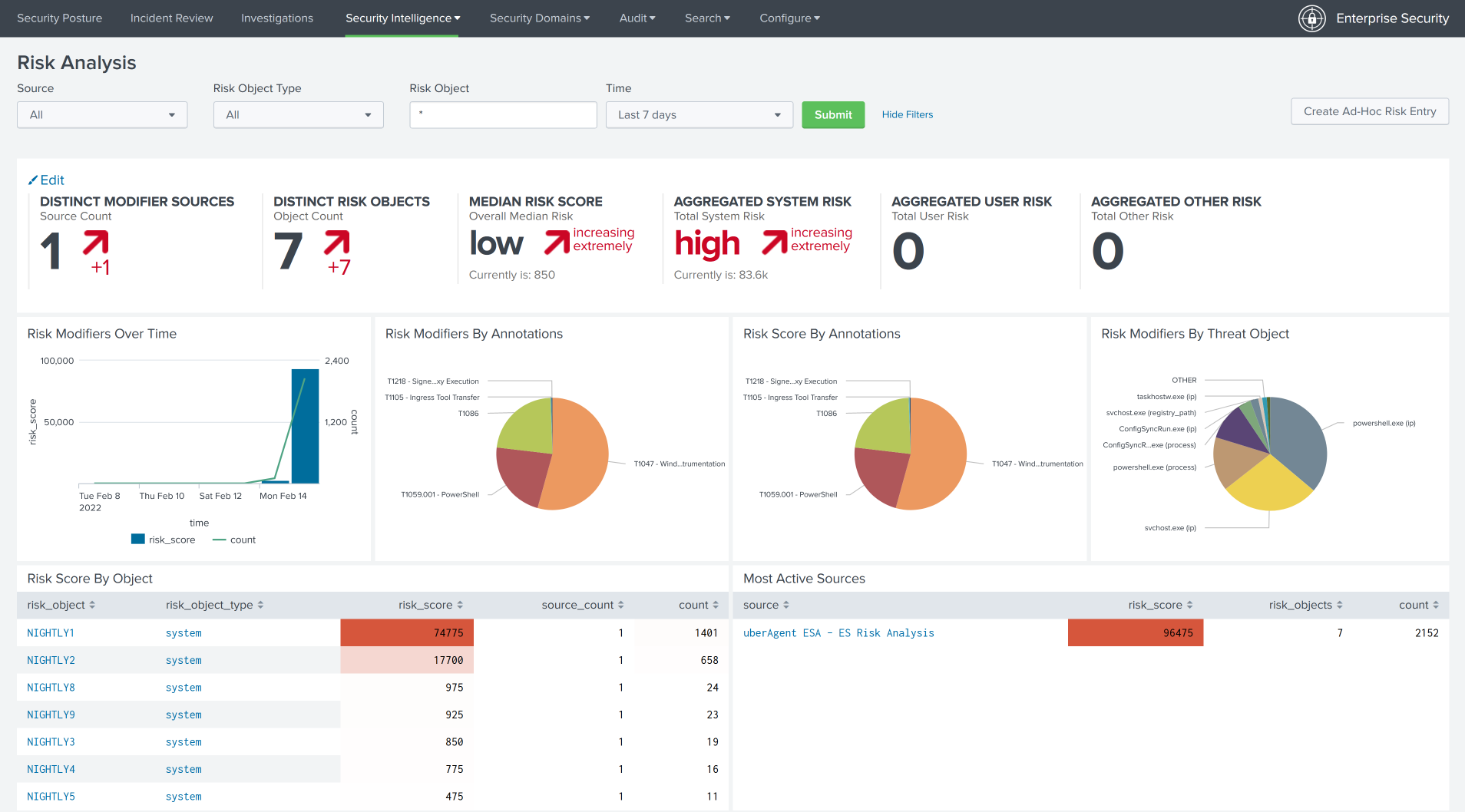
Splunk introduced risk-based alerting (RBA) in ES to reduce alert volume and enhance security operations. uberAgent supports RBA through the uberAgent ESA ES companion app. See the installation section above for installation instructions. When all requirements are met, the Splunk Enterprise Security dashboard Risk Analysis is populated automatically with uberAgent data:
Security Frameworks
RBA supports annotations with cyber security frameworks like MITRE ATT&CK®, CIS 20, NIST Controls, and more. uberAgent does, too, and comes with ATT&CK annotation out-of-the-box. You may add other cyber security frameworks anytime.
Annotations are part of the ESA Threat Detection rule specification. Implementation details can be found here. Below is a rule sample:
[ActivityMonitoringRule]
# Detects suspicious DNS queries known from Cobalt Strike beacons
RuleName = Cobalt Strike DNS Beaconing
EventType = Dns.Query
Tag = cobalt-strike-dns-beaconing
RiskScore = 100
Annotation = {"mitre_attack": ["T1071", "T1071.004"]}
Query = (Dns.QueryRequest like r"aaa.stage.%" or Dns.QueryRequest like r"post.1%")
GenericProperty1 = Dns.QueryRequest
GenericProperty2 = Dns.QueryResponse