Internet Explorer: Distinguish Standalone and Edge IE Mode Starts
Internet Explorer has been with us for many years as the ever-present browser. Most people will agree that the relationship is quite ambivalent. Especially in the corporate world, Internet Explorer was and still is deeply rooted. Many companies have applications in use that were not only developed on the basis of Internet Explorer but would not work at all without it.
Background Information
End-of-Life for Internet Explorer Announced
As you may have noticed, Microsoft has announced that the Internet Explorer 11 desktop application will be retired and go out of support on June 15, 2022. The challenge is to identify the dependencies of existing web applications on Internet Explorer and, perhaps more importantly, which of these applications are actually still being used.
Capture Internet Explorer Starts: Standalone & Edge IE Mode
Typically, two scenarios are of interest. Either the user launches Internet Explorer, iexplore.exe, directly, or a website is launched within Microsoft Edge in Internet Explorer mode. We would like to be able to capture both and distinguish between them.
To do so, the command line of the process contains the necessary information. To get a better understanding, let us compare a direct Internet Explorer startup vs. one coming from Edge IE mode.
Standalone Internet Explorer Start
When Internet Explorer is launched as a standalone application, the command line looks as follows:
"C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:6456 CREDAT:9730 /prefetch:2
Internet Explorer Started in Edge IE Mode
In Edge IE mode, the command line of the embedded Internet Explorer executable looks as follows:
"C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:11244 CREDAT:75266 APPID:MSEdge /prefetch:2
As you can see, the additional parameter APPID:MSEdge can be used to distinguish between standalone IE and Edge IE mode.
Configuration Instructions
Activate uberAgent Feature: EnableExtendedInfo
uberAgent does not send the command line to the backend by default. The reason behind this is that we want to keep the generated data volume as low as possible (more information about managing the data volume can be found here). However, for this scenario, the command line is required. Activate EnableExtendedInfo via uberAgent.conf as shown below.
# Setting name: EnableExtendedInfo
# Description: Send detailed information about each started process to the backend, e.g. path, command line, process ID, parent ID. This also enables the population of the ProcGUID field in other sourcetypes, which can be used for detailed process instance tracking.
# Valid values: true | false
# Default: false
# Required: no
[ProcessStartupSettings]
EnableExtendedInfo = true
Configure uberAgent Feature: Event Data Filtering
uberAgent provides a feature called Event Data Filtering. It is a powerful filtering mechanism for the collected data that operates right on the endpoint. Please learn more about it in our documentation.
For this use scenario, Event Data Filtering allows us to reduce the additional data volume generated by activating by EnableExtendedInfo to an absolute minimum. Specifically, we only need the command line for the process iexplore.exe in the sourcetypes uberAgent:Process:ProcessDetail and uberAgent:Process:ProcessStartup.
Since the only extra fields of interest are ProcID, ProcGUID and ProcCmdline, everything else that is not needed can be removed. Please find the example configuration below. Save the content as uberAgent-eventdata-filter-vastlimits-Internet-Explorer.conf and place that file in the same directory as uberagent.conf.
[EventDataFilter]
# Unnecessary for this use case.
Action = clear
Sourcetype = Process:ProcessDetail
Field = ProcGUID
Query = true
[EventDataFilter]
# Unnecessary for any other process than iexplore.exe.
Action = clear
Sourcetype = Process:ProcessStartup
Field = ProcID
Field = ProcParentID
Field = SessionID
Field = ProcGUID
Field = SessionGUID
Field = ProcParentName
Field = ProcPath
Field = ProcCmdline
Field = ProcParentGUID
Query = ProcName != "iexplore.exe"
[EventDataFilter]
# Remove unnecessary fields for iexplore.exe itself.
Action = clear
Sourcetype = Process:ProcessStartup
Field = ProcParentID
Field = SessionID
Field = SessionGUID
Field = ProcParentName
Field = ProcPath
Field = ProcParentGUID
Query = ProcName == "iexplore.exe"Include the new configuration file by using the @ConfigInclude directive below. A good place for the include directive is in uberAgent-eventdata-filter.conf which also resides in the same directory as uberAgent.conf. Find out more about configuration file locations here.
# Additional fields for Internet Explorer analysis (requires EnableExtendedInfo to be enabled)
@ConfigInclude uberAgent-eventdata-filter-vastlimits-Internet-Explorer.conf platform=WindowsFinally, restart uberAgent with the new configuration in place and head over to Splunk.
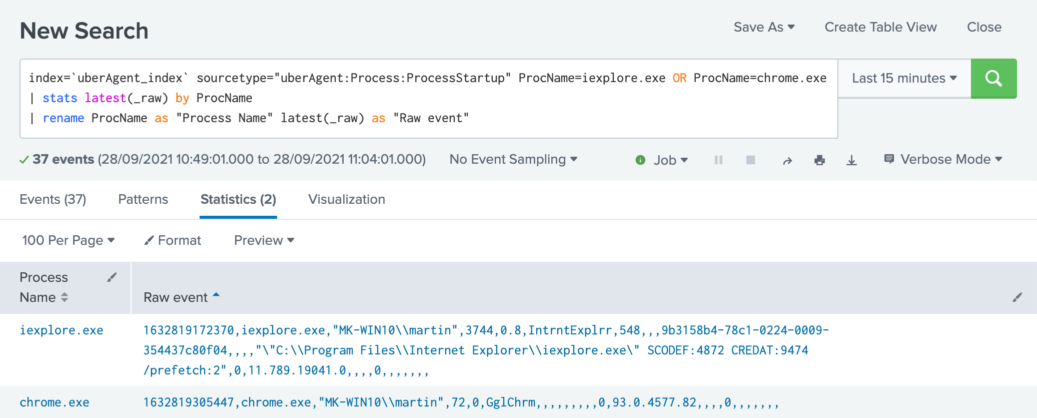
Verify Configuration
To prove our newly configured event data filtering works as expected, run the search below which highlights two raw events in Splunk. One for iexplore.exe and another one for chrome.exe. You can clearly see the difference in populated fields.
Splunk it!
Once the data is available in Splunk, it can be used to search for every direct or indirect Internet Explorer start, for every user on every host. In order to get the information about the actual web applications being used, the uberAgent browser add-on for Internet Explorer is required (documentation). This information is only available for direct Internet Explorer starts though, because of Microsoft Edge/Chromium API limitations.
The Search
| pivot `uA_DM_Process_ProcessStartup` Process_ProcessStartup
latest(AppName) as "App name"
latest(AppVersion) as "App version"
latest(_time) as StartTime
latest(ProcCmdline) as "Process Commandline"
latest(ProcID) as ProcID
filter host in ("*")
filter ProcName is "iexplore.exe"
splitrow ProcGUID
splitrow host as Host
splitrow ProcUser as "User name"
| join type=left Host, ProcID
[
| pivot `uA_DM_Application_BrowserPerformanceIE` Application_BrowserPerformanceIE
values(URL)
splitrow host as Host
splitrow ProcID
| fields + *
]
| eval "Start time" = strftime (strptime (StartTime, "%Y-%m-%dT%H:%M:%S.%Q%z"), "%Y-%m-%d %H:%M:%S")
| eval "Started via Microsoft Edge"=if(like('Process Commandline', "%APPID:MSEdge%"), "Yes", "No")
| eval "Web App (direct Internet Explorer starts only)"=nullif('values(URL)',"none")
| sort - "Start time"
| table "Start time", Host, "User name", "App name", "App version", "Started via Microsoft Edge", "Web App (direct Internet Explorer starts only)"
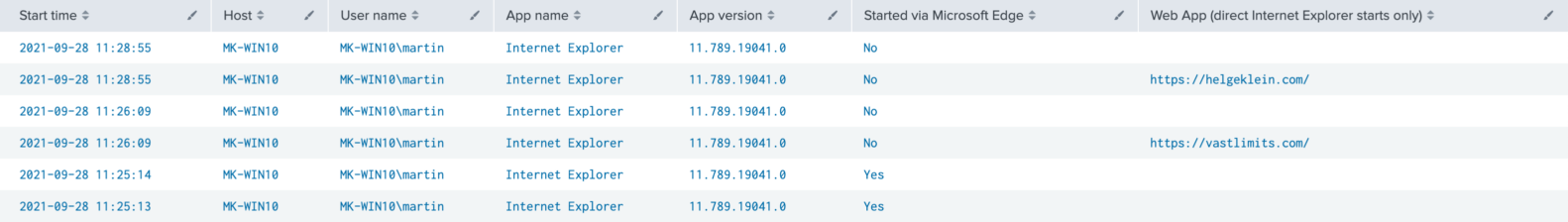
The Results
The resulting table shows for each instance of iexplore.exe whether it was launched standalone or via Edge IE mode (column “Started via Microsoft Edge”). For standalone IE processes that are used to rendering a web page, the URL is displayed, too.