User & Host Tags
uberAgent collects an extensive list of metrics. Pre-built Splunk dashboards allow you to filter the data by computer name, hardware manufacturer, IP address, or user, to name just a few of the available filtering options.
Businesses often store data about a machine’s build in the device’s registry. User information, on the other hand, is typically managed in Active Directory (e.g., the user’s department).
uberAgent’s user & host tags feature allows you to integrate custom identifiers in such a way that dashboards can be filtered by their values.
Here is an example: your organization stores the version of a machine’s OS image in a registry value on each machine. If you configure uberAgent to pick up that image build version through a host tag, you can filter the uberAgent dashboards by the version of your OS images. This allows you to determine if a new issue you are analyzing was introduced with a recent OS image, for example.
Tag Sources
Supported sources for tags are:
- Active Directory attributes
- Environment variables
- Registry values
These sources can be queried either per user or per computer.
Requirements
- uberAgent version 5.3 or later
- Host tags are determined directly after the Machine Inventory metric and are internally bound to it. If the Machine Inventory metric is not enabled in the configuration, host tags are not determined. Machine Inventory is enabled by default.
- User tags are determined directly after the user’s logon has finished and then every 15 minutes
Configuration
To configure the tags feature you can either use the configuration file or group policy. In this article, we are using the configuration file.
The stanza of interest in the configuration file is [UserHostTagging]. You can have multiple of these, one for each tag you want to set. The configurable settings are:
- Tag name
-
- A user-defined unique name of the tag. Spaces are permitted.
- This is the tag you can search for later in the dashboards.
- Example:
Department
- Tag type
-
- Defines if the tag is a host or a user tag
- Valid values:
Host,User - Example:
User
- Tag source
-
- Defines the source where the tag data is read from. Registry values of type
REG_EXPAND_SZare automatically expanded. - Valid values:
Registry,Environment,Ad - Example:
Registry
- Defines the source where the tag data is read from. Registry values of type
- Tag value
-
- The source element/path to read the tag’s data from.
- Registry format: any registry path, e.g.,
HKCU\Software\vast limits\Department(supported hives:HKLMandHKCU) - Environment variable format: the variable name enclosed in percent signs, e.g.,
%DEPARTMENT% - AD format: just the attribute name, e.g.,
Department
With the examples from above, you would get the following stanza:
[UserHostTagging]
Tag name = Department
Tag type = User
Tag source = Registry
Tag value = HKCU\Software\vast limits\DepartmentAnother example: group machines by roles like notebook, graphics workstation, desktop PC, virtual machine, or executive machine with an environment variable.
[UserHostTagging]
Tag name = Machine role
Tag type = Host
Tag source = Environment
Tag value = %MACHINEROLE%You can find more examples in our practice guide on the subject.
Usage in Splunk
The capability to filter for tags is built into the dashboards since version 5.3. To filter for host tags choose the Host tags filter field and to filter for user tags choose the User tags filter field.
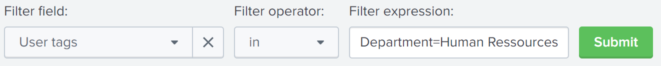
When using our user tag Department from above a search for all users from human resources would look like this:
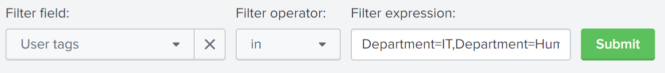
You can also search for users from two or more departments by listing them comma-separated.
Interested in all users where Department has a value (is not null)?
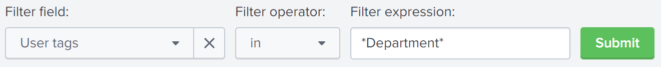
Note the asterisks around the tag’s name. This is needed by design when searching for the tag’s name only.