uberAgent Log Collector Splunk App
uberAgent maintains a very detailed and informative log file that can tell you a lot not only about uberAgent’s health but also about the machine uberAgent is running on. Naturally, the log file is stored locally on the computer uberAgent is running on which makes analysis and troubleshooting a bit difficult in large environments. But luckily it is very easy to solve that problem with Splunk!
What is it?
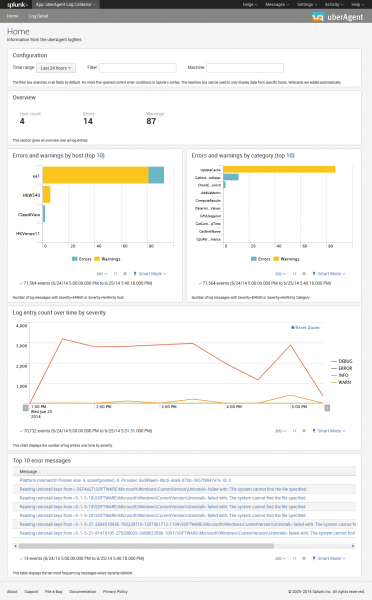
uberAgent Log Collector is a set of associated Splunk apps that collect the data logged by uberAgent, send it to Splunk for indexing and provide dashboards for easy access.
Installation
uberAgent Log Collector consists of the actual app containing the dashboards, a supporting add-on (SA) that creates the index and a technology add-on (TA) for collecting the data. These three components need to be installed on the following systems:
- App: search head(s)
- SA: indexer(s)
- TA: endpoints where uberAgent is deployed
uberAgent Log Collector Search Head App
Data Model Acceleration
Enable acceleration for the uberAgent Log Collector data model. Please follow the Splunk documentation for guidance.
uberAgent Log Collector Indexer App
Index Creation
Manually create the uberAgent Log Collector index. This can be achieved by using Splunk Web and the steps provided here. Use the following settings.
- Index Name: ua_meta_log
- Index Data Type: Events
- App: uberAgent_logcollector_SA
indexes.conf example:
[ua_meta_log]
homePath = $SPLUNK_DB/ua_meta_log/db
coldPath = $SPLUNK_DB/ua_meta_log/colddb
thawedPath = $SPLUNK_DB/ua_meta_log/thaweddb
maxMemMB = 20
maxConcurrentOptimizes = 6
maxHotIdleSecs = 86400
maxHotBuckets = 10
maxDataSize = auto_high_volume
repFactor = autoSystem Requirements
The TA requires Splunk’s Universal Forwarder to be installed on the same machine.
Download
The uberAgent Log Collector apps are available in the Splunk App Directory:
- Download uberAgent Log Collector app
- Download uberAgent Log Collector SA
- Download uberAgent Log Collector TA