Announcing the uberAgent ESA Config & Detection Rule Repo
We believe in openness, particularly when it comes to IT security. Where other products favor the “secret sauce” recipe, obscuring the limits of their capabilities and lulling customers into a false sense of security, uberAgent ESA offers a menu of transparent detection rules that are easy to comprehend, maintain, and extend. We’re happy to announce that the repository for these rules is now public.
Contents of the uberAgent ESA Rules Repository
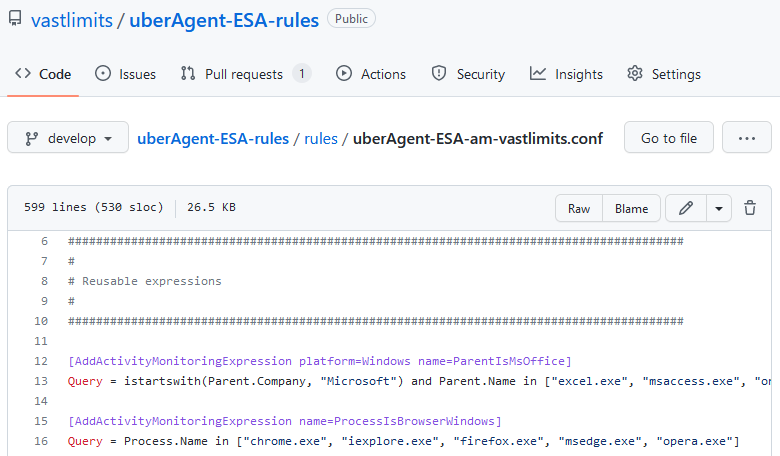
The uberAgent ESA rules GitHub repository, vastlimits/uberAgent-config, is the single source of truth for all uberAgent ESA configurations and detections.
Some of the rules in the uberAgent ESA repository are derived from Sigma signatures. These rules are updated daily from the latest sources in the Sigma project.
Structure of the uberAgent ESA Rules Repository
Git Branches = uberAgent Product Versions
The uberAgent ESA rules repository is designed to facilitate finding the latest rules for a given uberAgent version. In the repo, product versions are represented by Git branches. Each Git branch contains rules that are compatible with the matching uberAgent release.
Example: rules for uberAgent 6.2.x are located in the Git branch version/6.2, whereas rules for uberAgent 7.0.x are located in the Git branch version/7.0. Rules for the uberAgent version currently in development are found in the develop branch.
Folder Structure
The repository’s folder structure is kept deliberately simple. The subfolder rules is the principal place of interest. It hosts the configuration files that contain the detection rules and related configuration settings for uberAgent ESA.
Updating uberAgent ESA Detection Rules From the Repository
When you download and install uberAgent, it comes fully configured with the configuration that was current at the time of release. Newer configurations are published in the uberAgent ESA rules repository. We recommend periodically updating the endpoint agent with the latest detections.
To update an agent’s detection rules, replace its configuration files with the updated versions of the same files from the repository and restart the agent. The main config file, uberAgent.conf, is not part of the repo and, therefore, is left untouched during the config update.
Hint: shortly, we’ll announce a new feature that greatly simplifies the task of keeping thousands of endpoints updated.
Contributing to the uberAgent ESA Rules Repository
In the spirit of openness and collaboration, community contributions to the uberAgent ESA rules repo are encouraged. Before we can accept your pull request, we’ll ask you to sign a contributor license agreement so that we can freely distribute your contribution to all uberAgent users.
About uberAgent
The uberAgent product family offers innovative digital employee experience monitoring and endpoint security analytics for Windows and macOS.
uberAgent UXM highlights include detailed information about boot and logon duration, application unresponsiveness detection, network reliability drill-downs, process startup duration, application usage metering, browser performance, web app metrics, and Citrix insights. All these varied aspects of system performance and reliability are smartly brought together in the Experience Score dashboard.
uberAgent ESA excels with a sophisticated Threat Detection Engine, endpoint security & compliance rating, the uAQL query language, detection of risky activity, DNS query monitoring, hash calculation, registry monitoring, and Authenticode signature verification. uberAgent ESA comes with Sysmon and Sigma rule converters, a graphical rule editor, and uses a simple yet powerful query language instead of XML.
About vast limits
vast limits GmbH is the company behind uberAgent, the innovative digital employee experience monitoring and endpoint security analytics product. vast limits’ customer list includes organizations from industries like finance, healthcare, professional services, and education, ranging from medium-sized businesses to global enterprises. vast limits’ network of qualified solution partners ensures best-in-class service and support anywhere in the world.


